eDiscovery Trends: Tom O’Connor of Gulf Coast Legal Technology Center

This is the eighth of the LegalTech New York (LTNY) Thought Leader Interview series. eDiscoveryDaily interviewed several thought leaders at LTNY this year and asked each of them the same three questions:
- What do you consider to be the current significant trends in eDiscovery on which people in the industry are, or should be, focused?
- Which of those trends are evident here at LTNY, which are not being talked about enough, and/or what are your general observations about LTNY this year?
- What are you working on that you’d like our readers to know about?
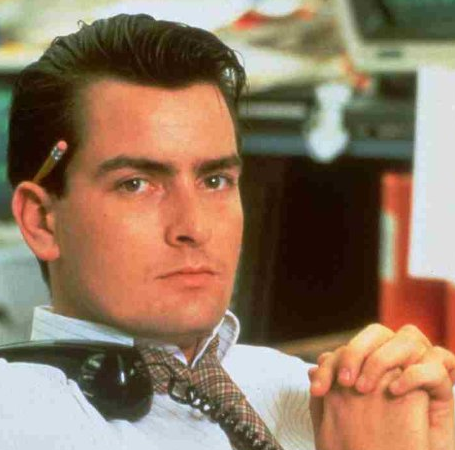
Today’s thought leader is Tom O’Connor. Tom is a nationally known consultant, speaker and writer in the area of computerized litigation support systems. A frequent lecturer on the subject of legal technology, Tom has been on the faculty of numerous national CLE providers and has taught college level courses on legal technology. Tom's involvement with large cases led him to become familiar with dozens of various software applications for litigation support and he has both designed databases and trained legal staffs in their use on many of the cases mentioned above. This work has involved both public and private law firms of all sizes across the nation. Tom is the Director of the Gulf Coast Legal Technology Center in New Orleans.
What do you consider to be the current significant trends in eDiscovery on which people in the industry are, or should be, focused?
I think that there is still a lack of general baseline understanding of, not just eDiscovery principles, but technology principles. Attorneys have been coming to LegalTech for over 30 years and have seen people like Michael Arkfeld, Browning Marean and folks like Neil Aresty, who got me started in the business. The nouns have changed, from DOS to Windows, from paper to images, and now its eDiscovery. The attorneys just haven’t been paying attention. Bottom line is: for years and years, they didn’t care about technology. They didn’t learn it in law school because a) they had no inclination to learn technology and b) they didn’t have any real ability to learn it, myself included. With the exception of a few people like Craig Ball and George Socha, who are versed in the technical side of things – the average attorney is not versed at all. So, the technology side of the litigation world consisted of the lit support people, the senior paralegals, the support staff and the IT people (to the minimal extent they assisted in litigation). That all changed when the Federal Civil Rules changed, and it became a requirement.
So, if I pick up a piece of paper here and ten years ago used this as an exhibit, would the judge say “Hey, counsel, that’s quite a printout you have there, is that a Sans Serif font? Is that 14 point or 15 point? Did you print this on an IBM 3436?” Of course not. The judge would authenticate it and admit it – or not – and there might be an argument. Now, when we go to introduce evidence, there are all sorts of questions that are technical in nature – “Where did you get that PST file? How did that email get generated? Did you run HASH values on that?”, etc. And, I’m not just making this up. If you look at decisions by Judge Grimm or Facciola or Peck or Waxse, they’re asking these questions. Attorneys, of course, have been caught like the “deer in the headlights” in response to those questions and now they’re trying to pick up that knowledge. If there’s one real trend I’m seeing this year, it’s that attorneys are finally taking technology seriously and trying to play catch up with their staff on understanding what all of this stuff is about. Judges are irritated about it. We have had major sanctions because of it. And, if they had been paying attention for the last ten years, we wouldn’t be in the mess that we are now.
Of course, some people disagree and think that the sheer volume of data that we have is contributing to that and folks like Ralph Losey, who I respect, think we should tweak the rules to change what’s relevant. It shouldn’t be anything that reasonably could lead to something of value in the case, we should “ratchet it down” so that the volume is reduced. My feeling on that is that we’ve got the technology tools to reduce the volume – if they’re used properly. The tools are better now than they were three years ago, but we had the tools to do that for awhile. There’s no reason for these whole scale “data dumps” that we see, and I forget if it was either Judge Grimm or Facciola who had a case where in his opinion he said “we’ve got to stop with these boilerplate requests for discovery and responses for requests for discovery and make them specific”.
So, that’s the trend I see, that lawyers are finally trying to take some time to try to get up to speed – whining and screaming pitifully all the way about how it’s not fair, and the sanctions are too high and there’s too much data. Get a life, get a grip. Use the tools that are out there that have been given to you for years. So, if I sound cynical, it’s because I am.
Which of those trends are evident here at LTNY, which are not being talked about enough, and/or what are your general observations about LTNY this year?
{Interviewed on the final afternoon of LTNY} Well, as always, a good show. This year, I think it was a great show, which is actually a bit of a surprise to me. I was worried, not that it would go down from last year, but that we had maybe flattened out because of the economy (and the weather). But, the turnout was great, the exhibit halls were great, a lot of good information. I think we’re seeing a couple of trends from vendors in general, especially in the eDiscovery space. We’re seeing vendors trying to consolidate. I think attorneys who work in this space are concerned with moving large amounts of data from one stage of the EDRM model to another. That’s problematic, because of the time and energy involved, the possible hazards involved and even authentication issues involved. So, the response to that is that some vendors attempt to do “end-to-end” or at least do three out of the six stages and reduce the movement or partner with each other with open APIs and transparent calls, so that process is easier.
At the same time, we’re seeing the process faster and more efficient with increased speed times for ingestion and processing, which is great. Maybe a bigger trend and one that will play out as the year goes along is a change in the pricing model, clearly getting away from per GB pricing to some other alternative such as, maybe, per case or per matter. Because of the huge amount of data we have do so. But also, we’re leaving out an area that Craig Ball addressed last year with his EDna challenge – what about the low end of the spectrum? This is great if you’re Pillsbury or DLA Piper or Fulbright & Jaworski – they can afford Clearwell or Catalyst or Relativity and can afford to call in KPMG or Deloitte. But, what about the smaller cases? They can benefit from technology as well. Craig addressed it with his EDna challenge for the $1,000 case and asked people to respond within those parameters. Browning Marean and I were asking “what about the $500,000 case?” Not that there’s anything bad about low end technology, you can use Adobe and S1 and some simple databases to do a great job. But, what about in the middle, where I still can’t afford to buy Relativity and I still can’t afford to process with Clearwell? What am I going to use? And, that’s where I think new pricing and some of the new products will address that. I’ve seen some hot new products, especially cloud based products, for small firms. That’s a big change for this year’s show, which, since it’s in New York, has been geared to big firms and big cases.
What are you working on that you’d like our readers to know about?
I think the things that excite me the most that are going on this year are the educational efforts I’m involved in. They include Ralph Losey’s online educational series through his blog, eDiscovery Team and Craig Ball through the eDiscovery Training Academy at Georgetown Law School in June. Both are very exciting.
And, my organization, the Gulf Coast Legal Technology Center continues to do a lot of CLE and pro-bono activities for the Mississippi and Louisiana bar, which are still primarily small firms. We also continue to assist Gulf Coast firms with technology needs as they continue to rebuild their legal technology infrastructure after Katrina.
Thanks, Tom, for participating in the interview!
And to the readers, as always, please share any comments you might have or if you’d like to know more about a particular topic!