Mobile Data Matters: Because Your Phone Might Be the Star Witness
Insights from the Masters Conference – Denver | June 24, 2025 | Hosted by Fennemore Craig PC | Article by Sheila Sadaghiani
Last week at The Masters Conference in Denver, I sat in on a session that felt less like a legal panel and more like group therapy for those of us trying to tame the chaos of mobile data in eDiscovery. The message was clear: if you’re not thinking about mobile data, you’re already behind.
This panel was moderated by Chip Koons, CEO at Veracity Forensics and the panelists were Rick Clark, VP of Strategic Partnerships and Marketing at CloudNine, Melinda Redenius, Forensic Consultant at Veracity Forensics and Sean Solis, Counsel at BakerHostetler. This panel rounded out the perspectives of technology, forensics and the practice of law with the focus on smartphones in investigations and litigation.
Let’s face it, our smarty pants devices know everything. Who we texted, where we were, what we Googled at 2 a.m., and whether we really did hit our step count (thank you, Apple Watch). So, when a case lands on your desk and a smartphone or device is involved, and it always is, it’s time to get serious.
Phones Aren’t Just Phones Anymore
The session kicked off with a reminder that mobile devices are no longer simple communication tools. They are digital diaries overflowing with location data, app activity, messages, and maybe even a TikTok or two. That also means they are goldmines in investigations, but getting to that gold, not so easy.
Challenge #1: Privacy in a BYOD World
The ever-present Bring Your Own Device (BYOD) issue came up fast. The consensus? If you don’t have a crystal-clear policy in place, you’re setting yourself up for a compliance migraine.
Policy isn’t just a formality, it’s your defense. Require consent. Explain what’s being collected. And for the love of litigation, communicate with custodians. People get weird when you ask to peek into their phones, and can you blame them? Some even back up personal data to their iClouds, which just adds another layer of “fun.”
Also, heads up; board members are not always thrilled about handing over their devices. Shocking, I know.
One story shared involved a chemical plant incident where investigators suspected employees were texting during the event. They requested phone data leading up to and during the incident. The court said nope, calling it a fishing expedition. Moral of the story? Narrow your scope or risk reeling in an empty net.
Challenge #2: Ephemeral Everything
Next up: ephemeral data. Think Snapchat, disappearing messages, and auto-delete features that make forensic teams want to throw their phones into the nearest river.
But don’t lose hope. You can still get creative. One clever tactic mentioned was collecting data from other people the custodian communicated with. Deleted texts? Rebuild them from the other side of the conversation. Like digital duct tape.
Also, this is a big one, the Department of Justice is now specifically calling out the need to preserve ephemeral messages. So yes, your compliance program better have something to say about that.
Oh, and when you’re issuing a legal hold, spell it out. Literally. Include instructions on how to turn off auto-delete features. No assumptions.
Challenge #3: Geo-Location (aka “Where Were You Really?”)
Geo-location came up as both a powerful tool and a slippery slope. Every photo you take, some apps you open, it’s all tagging your location to the same database on the device. But here’s the twist: geo data is tied to the phone, not necessarily the person using it. So, you might know where the phone was, but can you prove who was holding it?
Still, if used wisely, location data can help build a compelling narrative. It just needs to be paired with the right context and a bit of tech wizardry.
Real Talk: No Easy Buttons
The overall vibe? There’s no magic wand here. But there are technologies that can help make sense of the chaos. Whether you’re threading messages across multiple platforms or using targeted collection tools like ModeOne, Oxygen, or Cellebrite, the key is to know your case and tailor your collection strategy accordingly. Then, review platforms like CloudNine Review will make the review experience MUCH easier than traditional document review platforms.
One case even hinged on data from a wearable fitness device. Yep, turns out those calories burned were worth more than expected in court.
Final Takeaways:
- Your mobile data strategy should be locked and loaded before discovery starts.
- Communication with custodians isn’t optional; it’s critical.
- Don’t just collect, preserve intentionally.
- And finally, get a service provider in early. This isn’t a solo mission.
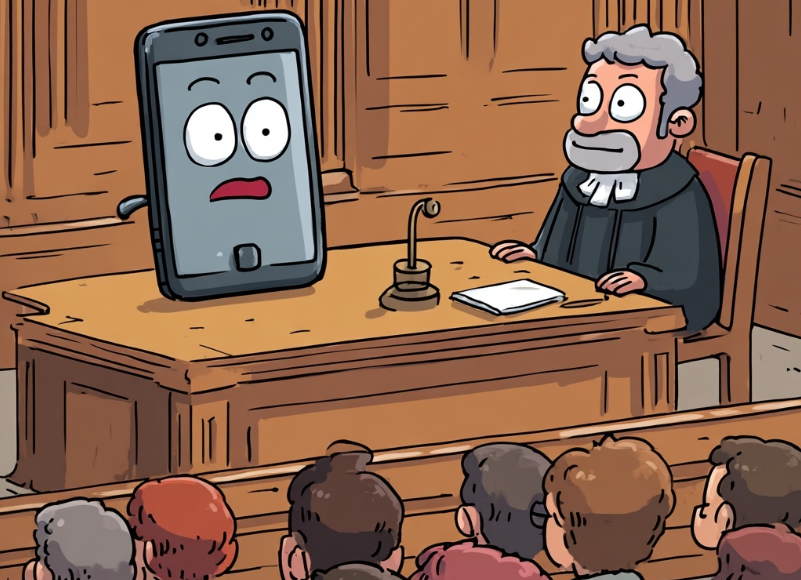
So, the next time someone shrugs off mobile data as “just texts,” remind them: your phone might be the most honest (and unforgiving) witness in the room.
P.S. If you think mobile discovery is scary now, just wait until someone subpoenas your smart fridge.