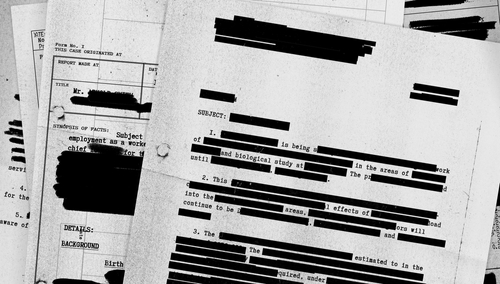
Per FRCP Rule 26(g), attorneys must sign discovery requests, responses, and objections. To the best of the attorney’s knowledge, the signature certifies three factors: 1) the document is compliant with existing rules and regulations; 2) it has no improper purpose such as slowing litigation; 3) it is not unreasonably burdensome to the producing party. This may become an issue if your client opts for self-collection. If counsel does not oversee or supervise the collection process, they have violated the rule and will be sanctioned accordingly. [1] During self-collection, custodians are responsible for identifying and gathering potentially relevant ESI on their own. When conducted carefully, self-collection may be adequate and cost-effective for small cases. However, there are several risks involved. The client may lose valuable metadata if their collection is done incorrectly. Additionally, they may purposely or accidentally omit incriminating evidence. Overall, if the self-collection process is not defensible and well-documented, the evidence will be rejected, and sanctions will follow. [2]
Self-Collection Cases and Sanctions
- EEOC v. M1 1500 Group is a well-known age discrimination case in which two of the defendant’s employees collected ESI without any counsel supervision. Counsel signed the discovery response despite their hands-off approach. The plaintiffs moved to compel after counsel admitted to their negligence and the defendants produced less evidence than expected. Judge Matthewman granted the defendants a second chance but required both parties to collaborate in a robust meet and confer. The court also issued sanctions and advised counsel to seek the assistance of an ESI vendor. [3]
- Over a year after the case ended, Green v. Blitz reopened once the court discovered that the defendant destroyed and omitted relevant email evidence. Only one employee oversaw the collection process, and he described himself in court as “computer illiterate.” After confirming the relevance of the missing emails, the court imposed civil contempt sanctions worth $250,000. The defendants also faced a $500,00 purging sanction unless they provided a copy of the order to all litigants who filed against them within the past two years. As the final sanction, Blitz USA was ordered to file a copy of the order when filing any lawsuit within the next five years. [4]
- Nat’l Day Laborer Org. v. U.S. Immigration and Customs Enforcement Agency involved various government agencies who lacked a uniform collection plan. The agencies also failed to properly document their differing collection processes. Consequently, the agencies were sanctioned for relying too heavily on self-collection. They were also reprimanded for their undocumented and uncoordinated efforts.
- In Suntrust Mortgage Inc. v. AIG United Guaranty Corp., the defendant chose not to seek the help of any forensic experts or ESI vendors. One employee was in charge of the identification and collection process. By copying and pasting different emails together, the employee tampered with the evidence before production. The fabrication resulted in court issued financial sanctions. [2]
Avoid self-collection pitfalls by utilizing CloudNine’s Collection Manager, a breakthrough extraction solution for Office 365 emails and OneDrive files. To learn more information or request a demo, visit: https://cloudnine.com/ediscovery-software/cloudnine-collection-manager/
[1] Gretchen E. Moore, “The Perils of Self-Collection of Electronically Stored Information,” The National Law Review, April 28, 2021.
[2] FindLaw Attorney Writers, “Self-Collection: The Good, the Bad, and the Ugly,” FindLaw, June 20, 2016.
[3] Kelly Twigger, “Beware of the Perils of Allowing Self-Collection,” eDiscovery Assistant, July 9, 2020.
[4] Peter Vogel, “Another Trap is Sprung: The Danger of Self-Collection,” Foley & Lardner LLP, June 20, 2011.